Octane has uncovered serious security vulnerabilities in Chromium, Gecko, and WebKit, the three browser engines that power 99.7% of web browser traffic.
Three Engines, One Web: Octane Finds Vulnerabilities in All Major Internet Browsers
Octane has uncovered serious security vulnerabilities in Chromium, Gecko, and WebKit, the three browser engines that power 99.7% of web browser traffic.
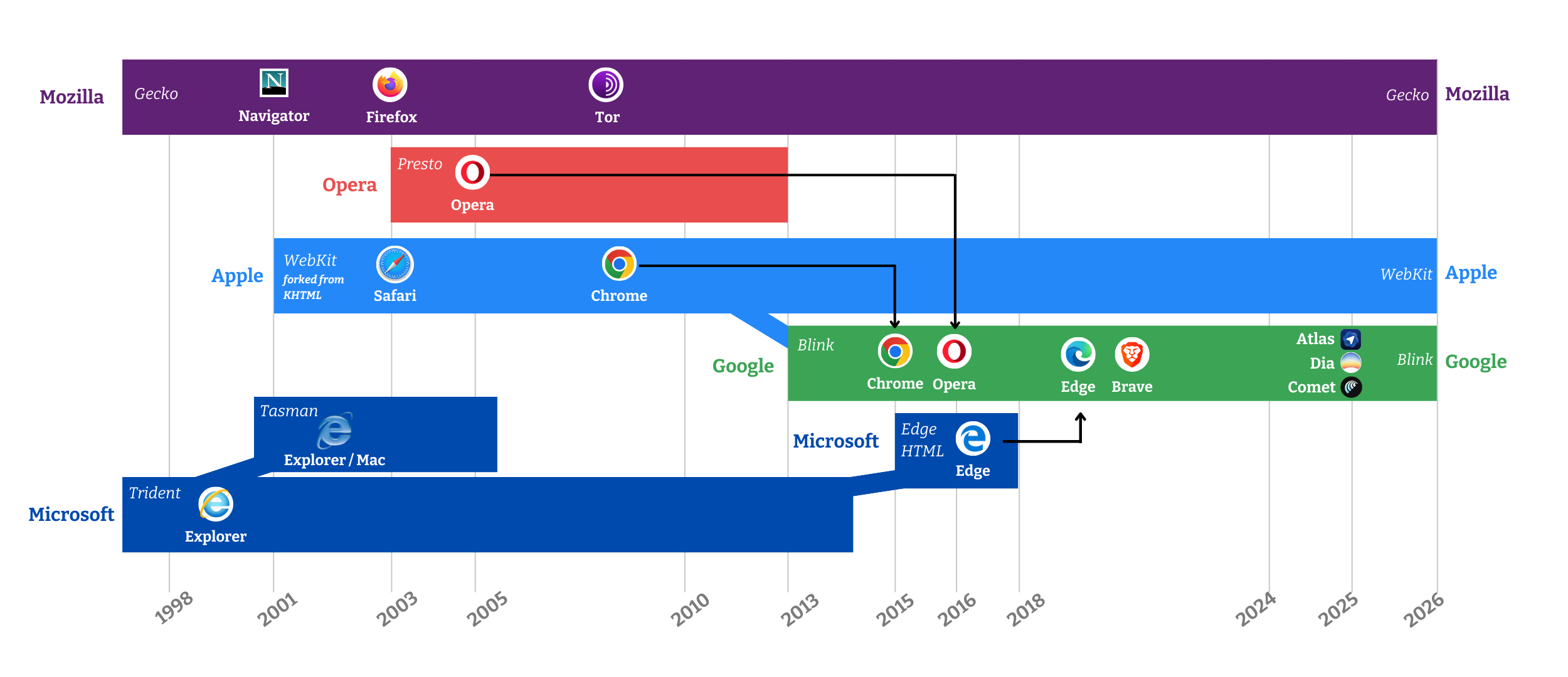
Three browser engines render nearly everything you see on the web. Blink powers Chrome, Edge, Brave, Opera, and all other Chromium-based browsers. Gecko powers Firefox. WebKit powers Safari, and under Apple’s platform rules it also underlies other browsers on iOS. Together, they account for 99.7% of global browser traffic. Much of the modern web, from banking and messaging to medical records, onchain wallets, and corporate infrastructure, depends on these three codebases stewarded by Google, Mozilla, and Apple.
.jpg)
This centralization leads to certain efficiencies as standards converge and compatibility improves. But the security case is much less comforting. A single bug that slips into any one of those codebases becomes a live risk for billions of users as soon as it lands in a stable release of any major browser.
Octane found serious vulnerabilities in all three.
One Vulnerability Class, Three Browser Engines
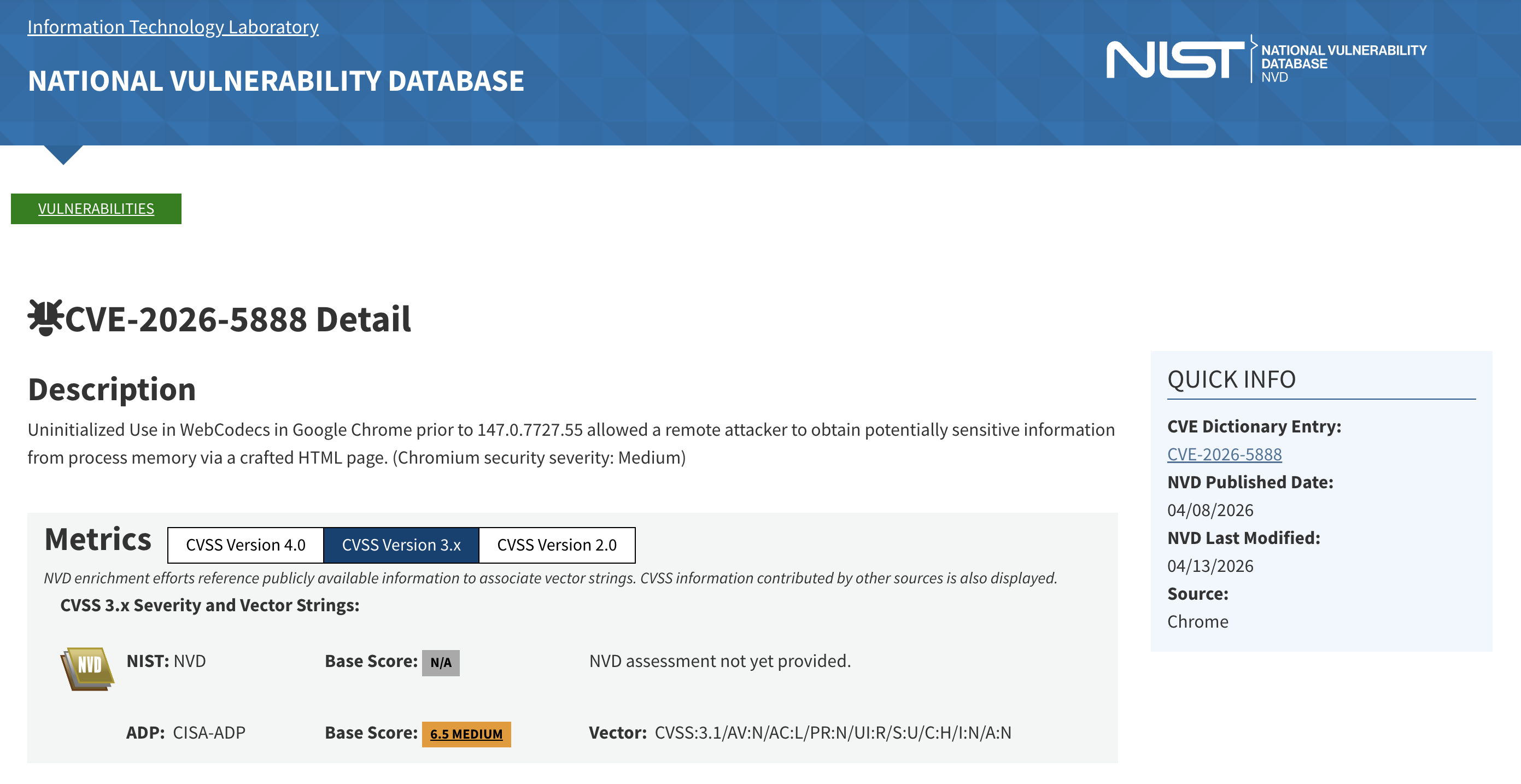
Chromium: CVE-2026-5888. Octane found a heap disclosure in WebCodecs, reachable through VideoFrame.copyTo(codedRect). A malicious page could request a pixel copy using a rectangle that exceeded the frame's legitimate bounds and receive, in return, uninitialized bytes from renderer memory that JavaScript was never intended to see. The bug was reported to Google's Bug Hunters Chrome Vulnerability Report Program, triaged at P2/S2, and is now fixed.
Gecko: Octane produced multiple heap disclosures across canvas, image, and media paths. The pattern rhymes with the Blink finding: stride mismatches, missing bounds checks, and off-by-one indexing in performance-critical routines that move decoded media into buffers the page is allowed to read. Each bug exposed adjacent heap memory instead of the narrow slice the page should have been able to access.
WebKit: The reported issues are currently being remediated. Apple’s Product Security team has reproduced the reports and is actively working through them. We’ll share specifics once fixes are live and responsible disclosure permits it.
The mechanics differ somewhat, but the vulnerability class is consistent across all three engines. These bugs can leak:
- fragments of image and video buffers tied to other origins or adjacent state,
- memory addresses that reveal renderer layout,
- and bytes that should never cross the browser’s internal boundaries.
None of these bugs, on their own, hand an attacker complete control over your machine. What they do enable are downstream exploit chains that utilize these vulnerabilities to perform more sophisticated and damaging actions.
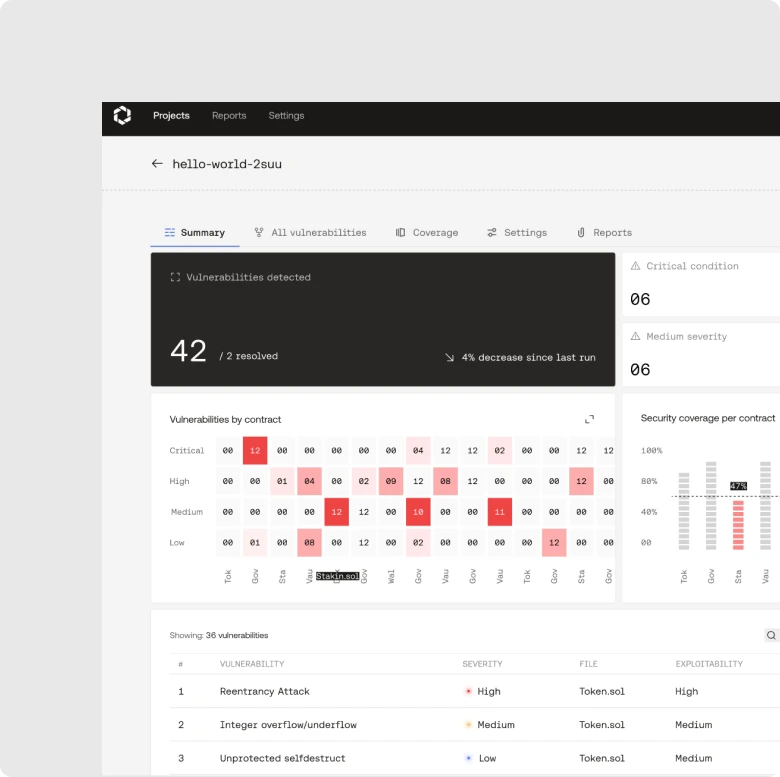
From Smart Contracts to Application Security
Octane began in smart contract security. The onchain threat model is particularly harsh: code is public, deployments are usually immutable, and an exploit finalizes in the time it takes a chain to confirm a block. There is no patch window, no mean-time-to-remediation, no reassurance that a fix in the next release will catch most of the blast radius. A missed bug is a realized loss, denominated in dollars, that afternoon.
That environment forces security researchers to reason about code the way an adversary does. That means both structurally and across multiple layers of abstraction, rather than against a simple checklist. It produces the kind of security analysis that has to lead to real results, because the alternative is being wrong on a public block explorer – forever.
These browser findings are the proof that this approach does generalize.
Browser engines are not low-hanging fruit. They are among the most heavily scrutinized software systems in the world: written by elite systems engineers, fuzzed continuously, audited continuously, and targeted constantly by both bounty hunters and state-backed threat actors.
What transferred from smart contracts to browser engines was a specific way of seeing. Octane’s analysis learned from one of the most adversarial environments online – crypto – and we’re now applying it to the fundamental infrastructure we all rely on.
Who Finds Your Bugs First?
Every non-trivial codebase contains bugs. The question is not whether they exist, it’s whether you find them before your adversaries do.
Octane is an AI-native offensive security company. We first applied our analysis to smart contracts because the onchain threat model is unforgiving enough to make better researchers of everyone who works in the field. We then brought Octane to the baselayer and found a high-severity vulnerability in the second-largest Ethereum execution client. Browser engines were the next test of whether our onchain training transferred to the rest of the stack, and the CVE and bug trackers at Google, Mozilla, and Apple are the proof that it does.
If you're building applications people truly rely on, talk to us today.