Spark integrated Octane across three critical repositories to establish continuous, AI-driven security analysis at the pull request level. Octane embeds offensive security review into the development workflow itself, before code reaches production or is sent off to an auditor.
How Spark Uses AI to Secure Billions in DeFi
Spark integrated Octane across three critical repositories to establish continuous, AI-driven security analysis at the pull request level. Octane embeds offensive security review into the development workflow itself, before code reaches production or is sent off to an auditor.
Octane has found one or two of these [issues] where I've been extremely impressed, where I'm like, "This is equivalent to a world-class auditor."
Lucas Manuel, Co-Founder and Head of Smart Contracts at Phoenix Labs, developer of Spark and Maker

Security That Keeps Pace with Development
Spark is one of the largest DeFi protocols by total value locked, with infrastructure spanning lending, savings, and liquidity deployment across multiple EVM chains. At the time of writing, the protocol’s major components included approximately $1.9 billion in SparkLend, $3.9 billion in Spark Savings, and $1.6 billion in the Spark Liquidity Layer.
.png)
Spark is an entire integrated onchain financial system. SparkLend provides borrowing and lending markets, Spark Savings enables users to deposit DAI or USDS into yield-bearing vaults, and the Spark Liquidity Layer allocates stablecoin liquidity across chains and venues. Together, these systems form a large and evolving onchain platform built on high-quality collateral, deep stablecoin liquidity, and cross-chain capital movement.
Spark’s security posture reflects this multi-billion dollar responsibility to depositors. The protocol was built on the foundation of Aave v3’s battle-tested architecture, then extended with custom modules for rate control, savings infrastructure, and liquidity management. It maintains conservative risk parameters, limits collateral exposure to blue-chip assets, and supports its security program with professional audits and a live bug bounty.
But point-in-time review alone is not enough for a protocol that continues to push updates.
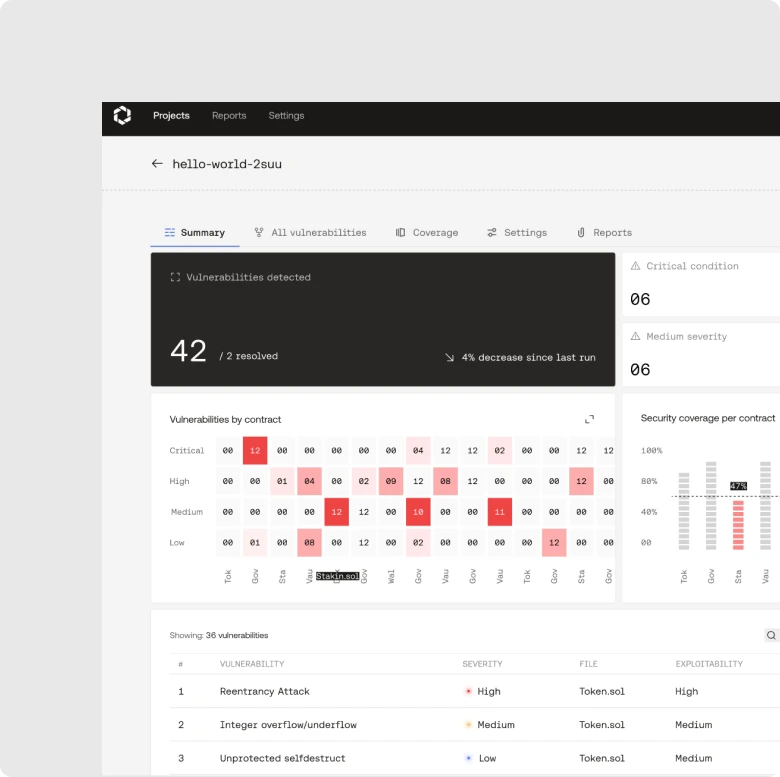
The Solution: Octane's Continuous Offensive Security Layer
To strengthen security earlier in the software lifecycle, Spark integrated Octane across three key repositories:
With Octane integrated into CICD, Spark receives continuous offensive security analysis on every pull request – before code updates progress further downstream. Potentially risky code paths can be flagged as soon as they are introduced, rather than weeks later during a late-stage review. This gives the development team a much tighter feedback loop and helps reduce the operational and financial costs of surfacing issues right before release.
To date, Octane has run:
- 62 scans on spark-alm-controller
- 11 scans on spark-spells
- 2 scans on sparklend-cap-automator
That’s 75 total scans across three codebases, with no critical vulnerabilities detected to date.
For Spark, the value is not in replacing its existing security controls entirely, but rather in strengthening an already-mature security posture with continuous pre-deployment coverage.
Audits and bug bounties still have their place. Conservative protocol design remains crucial. But Octane adds another critical layer: continuous analysis inside the development workflow itself.
This matters for any protocol operating at Spark’s scale. As digital asset infrastructure matures, attracts capital, and interoperates with other systems, software security needs to move at the same pace. Code needs continuous review to stay secure across dynamic repos, interconnected modules, and live blockchains.
“Our security program has always been built around defense in depth. We combine careful protocol design, professional audits, and a live bug bounty. What Octane adds is coverage between those controls: continuous analysis at the moment new code is introduced. That kind of continuous coverage fundamentally changes the economics of finding and fixing issues.”
– Lucas Manuel, Co-Founder and Head of Smart Contracts at Phoenix Labs, developer of Spark and Maker
Why This Matters for Digital Asset Infrastructure
As traditional financial institutions come onchain – with custody, tokenized assets, stablecoin settlement, and direct protocol participation – the security of that infrastructure must be evaluated on terms that match the stakes.
The questions that matter are the same ones that apply to any trading system, custody platform, or settlement layer:
- What is the attack surface?
- How is code reviewed before deployment?
- What is the coverage between point-in-time audits?
- How quickly can vulnerabilities be detected and addressed?
Spark's integration of Octane answers those questions. Continuous, automated, adversarial code review, running on every proposed change across the repositories that underpin billions in assets, represents the kind of security discipline that serious counterparties expect from the onchain infrastructure they interact with.